Student Job Offers Scams
Jobs that sound too good to be true should raise a red flag for any college student. Fake job postings abound in unsolicited emails sent to your student account and on online job listing sites. Fake jobs can be attempts to steal personal information about you or steal money or bank account information from you. You could also get entangled in criminal activity, so be cautious.
These attacks are on the rise and often employ multiple methods to make email recipients think that the emails are legitimate. Sometimes scammers impersonate instructors, deans, or other members of the LMU/LLS community to trick students and employees into giving up personal information. For example, a job or internship scam attempt may spoof the sender’s name, using lmu.edu in the email address (e.g., dean.lmu.edu@gmail.com).
As a rule, students are only hired for LMU/LLS student jobs through official channels like Handshake, LMU’s internships job site and Workday, work study students job posting site.
To protect yourself from job scams involving someone pretending to be an LMU/LLS community member, do not respond to any unsolicited emailed job offers without verifying through an official source, such as a LMU/LLS department website, Handshake, Workday, or Human Resources. The same applies to text messages, even if the sender claims to be someone you know from LMU/LLS.
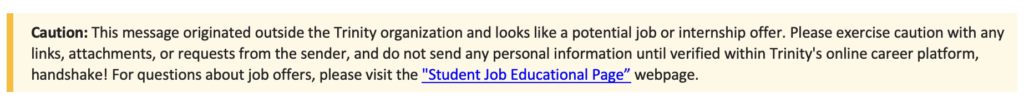
External Email Job Offer Warning Banner
ITS has introduced a new feature in the email system that will notify students of emails from outside the LMU and LLS community members. This change is being made to make it easier for anyone identify potential job and internship scam emails. The banner will appear in the first line of the body of the email and will include the following message:
Here are some tips to help you identify fake jobs. You should always carefully research the legitimacy of employers before applying.
Common Job Scams Targeting College Students:
- Mystery shoppers
- Envelope stuffing from home
- Repackaging or shipping from home
- Issuing checks/check processing from home
- Model/talent agencies
- Pyramid sales schemes
- A variety of scams where a student is asked to pay for certification, training materials, or equipment with the promise of reimbursement
- Pet Sitting/Babysitting
- Amazon purchases
Overpayment Scams
- Watch out for over-payment scams. These are often posted as bookkeepers, personal assistants, administrative assistants, etc., to assist in processing checks or mystery/secret shoppers. The “company” sends a check to the “assistant” (student), who is then responsible for taking their”salary” out of the check and wiring the remainder of the money back to the “company.” These checks are fraudulent and can leave you out thousands of dollars and face criminal charges.
Beware if the Email or Job Posting:
- Does not indicate the company name
- Comes from an email address that doesn’t match the company name
- Does not give the employer contact information, title of the person sending the email, company address, phone number, etc.
- Offers to pay a large amount for almost no work
- Offers you a job without ever interacting with you
- Asks you to pay an application fee
- Wants you to transfer money from one account to another
- Offers to send you a check before you do any work
- Asks you to give your credit card or bank account numbers
- Asks for copies of personal documents
- Says you must send payment by wire service or courier
- Offers you a large payment for allowing the use of your bank account, often for depositing checks or transferring money
- Sends you an unexpectedly large check
- No legitimate employer will send payment in advance and ask the employee to return a portion of it.
- DO NOT provide any personal information, especially Social Security numbers or financial information!
Email Impersonation Scams
Since COVID-19, LMU has seen an increased number of fraudulent emails, or SPAM messages, designed to trick recipients into clicking links, opening attachments, or taking other actions. Specifically, we have seen a large number of Email Impersonation Scams targeting key individuals within the university. These attacks typically seem to come from personnel in positions of authority and ask targets to perform money transfers, pay invoices, or send sensitive data.
To learn more about how to recognize these phishing emails and protect yourself and our organization from getting hooked, read the following list of key phishing identifiers:
1. Suspicious Email Addresses - If an email seems to be from a legitimate source by came from a nonofficial doman (i.e., @hotmail.com instead of @lmu.edu), it's probably fraudulent. Also check other recipients of the email - if it was sent to a lot of people, especially ones you don't know, you should be suspicious.
2. Generic Salutations - You should be suspicious of any email that isn't addressed directly to you. Watch out for salutations like "Dear Madam" or "Valued Customer".
3. Spelling Mistakes and Grammatical Errors- Everyone makes mistakes, but glaring and obvious errors such as "Loyola Mary Mount University" or a plethora of spelling mistakes and grammatical errors are reasons be wary.
4. Immediate Action Required- Phishing emails frequently have an alarmist tone, to try to rush recipients into taking action and making mistakes. Legitimate organizations rarely ask for immediate action or personal information.
5. Suspicious URLs - If you hover your cursor over a link, the destination will appear; phishing emails often use URL text in emails that seems legitimate, but directs to not-secure sites.
6. Attachments - As a general rule, don't open attachments you aren't expecting. If you get a strange attachment from someone you know, contact them before opening it.
7. Too Good To Be True - If something seems too good to be true, it probably is, especially if you receive offers from companies or services you've never used, or get prizes from a contest you never entered.
8. Weird Messages From Friends - Phishing emails may come from someone you know, if a friend's email has been hacked or if a hacker created a new email address using a friend's name to try to trick recipients. If you receive a suspicious email from a friend, call or text them about it before opening the message.
LMU ITS Pyramid from LMU ITS on Vimeo.
Phishing Awareness Program
Phishing continues to be a threat to our campus. A successful phishing attack can lead to loss of research, system failures across campus, fraud, financial scams, and more. Phishing emails are becoming more common and sophisticated. It is important for us to know how to protect ourselves against them.
LMU's Phishing Awareness program periodically sends simulated phishing emails to campus community. The objectives of the campaigns are educational and designed to cultivate awareness. See the new LMU Phish Bowl for examples of phishing emails sent to members of the campus community.
Program Objectives: